by Noufal Radhitya, Threat Intelligence Intern @ PT ITSEC Asia Tbk
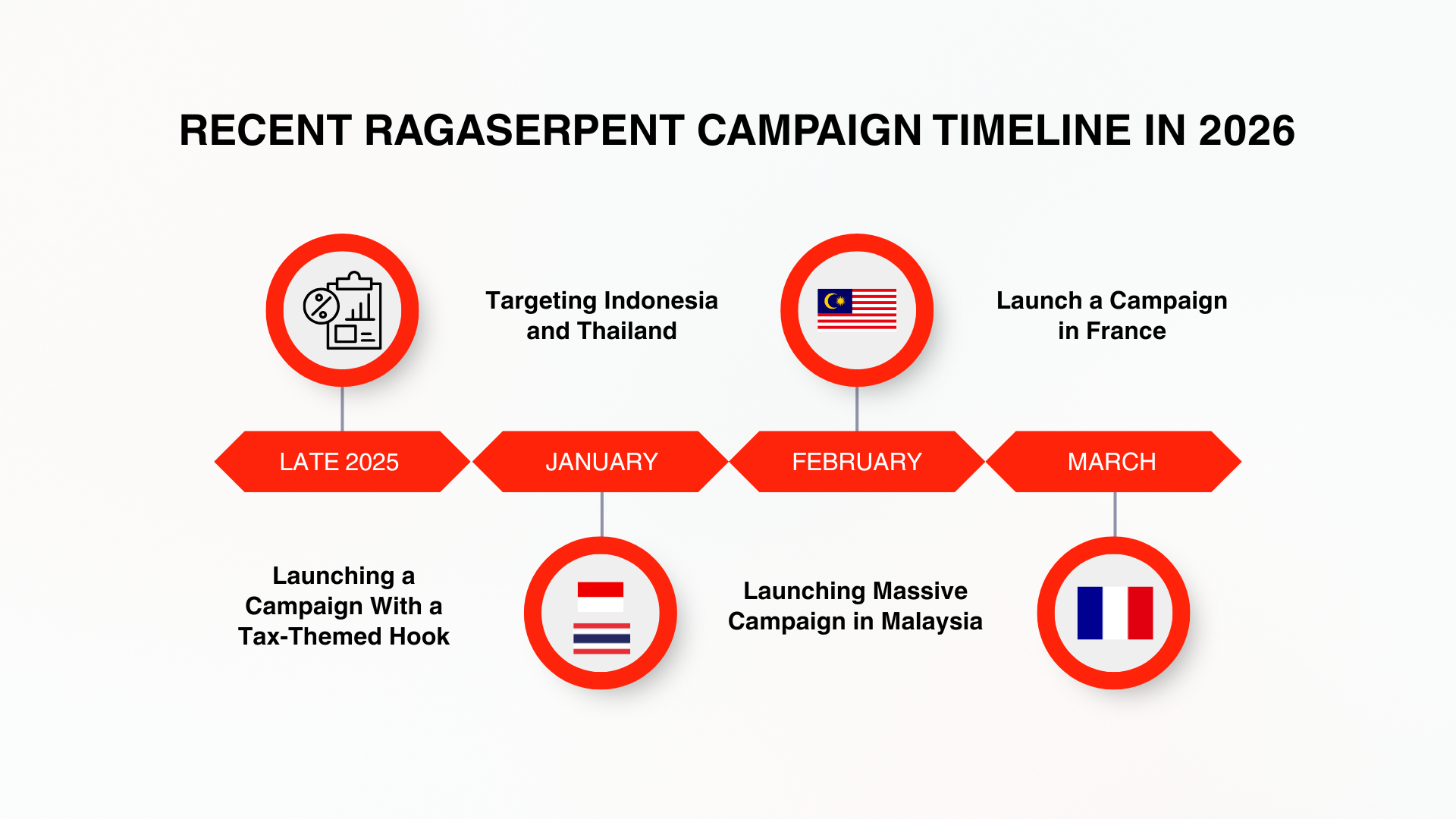
Throughout 2025–2026, tax-themed malware campaigns linked to the MITRE ATT&CK group SideWinder (G0121) commonly known as RagaSerpent—exhibited a high-tempo, cross-border attack pattern. Relying on spearphishing campaigns centered on audits and regulatory compliance, these campaigns successfully exploited targets’ trust to gain initial access effectively.
Building on findings from ITSEC Asia (February 2026), this latest research reveals new indicators of compromise (IOCs) and the evolution of increasingly adaptive attack techniques. Operating not only in Southeast Asia, such as Indonesia and Thailand recent activity indicates an expansion of targets to Malaysia and even France, signaling an increase in the scale of operations.
RAGASERPENT ACTIVITY
According to findings from ITSEC Asia (February 2026), initial victims were identified in India, Indonesia, and Thailand. Follow-up analysis in February to March 2026 shows expansion into Malaysia and France, indicating a broader geographic reach. The campaign maintains a consistent infrastructure strategy, including the use of free hosting services and rapid domain rotation to evade detection.
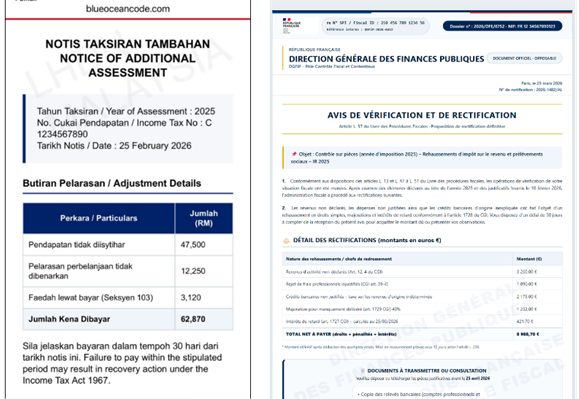
Recent phishing pages observed in India, Malaysia, and France demonstrate clear UI improvements, such as detailed payment elements and interfaces that closely resemble official government platforms. This evolution increases credibility and strengthens the effectiveness of social engineering, enabling RagaSerpent to sustain access and compromise targets by exploiting user trust at scale.
INFECTION CHAIN AND DETAIL INFORMATION
Interestingly, samples observed outside the usual targeting regions particularly in France, reveal subtle yet telling variations that signal an ongoing evolution in RagaSerpent’s delivery strategy. Two identified samples show the use of .vbs (Visual Basic Script) droppers with localized naming in both French and English, such as “AVIS D’IMPOSITION” and “Assessment Order,” enhancing their legitimacy for targeted victims. In one case, the dropper script retrieves a payload whose filename embeds an IPv4 address, for example 216.250.104.166ClientSetup.exe, indicating a deliberate attempt to blend infrastructure with delivery artifacts.
If you are interested in the complete technical analysis of this research, the full paper “Uncovering New Indicators in RagaSerpent’s ‘Tax Audit’ Malware Campaign” is attached to this article.
The paper provides comprehensive insights into the infection chain, infrastructure patterns, malware behavior, and newly identified indicators of compromise, along with a deeper breakdown of detection strategies and threat intelligence correlations.
The attached document includes detailed technical analysis, diagrams of the attack workflow, and a complete list of IOCs referenced in this summary.
This research highlights how adaptive threat actors like RagaSerpent continue to evolve their tactics, and how proactive threat intelligence can significantly improve detection, response, and overall cybersecurity resilience in modern environments.